
Maths in a minute: Maths and communication
A defining aspect of human society throughout the ages is our need to communicate. This trend has accelerated a great deal in recent years, with our instant access to huge amounts of data and the ability to communicate over vast distances via mobile phones. Sometimes we want our communications to be secret (such as when we send credit card details over the Internet), and sometimes we want them to be as clear as possible (such as when we use a mobile phone to talk to someone in Australia).
However, none of this would be possible without mathematics. The business of secret communications started with the early ciphers used, for example, by Julius Caesar. Although Caesar was not a mathematician, his ciphers certainly had a mathematical basis. They used addition modulo 26, which works like adding numbers on a 12-hour-clock, only instead of going back to 0 when you reach 12, you go back to 0 when you reach 26. Since then mathematics has played a part in nearly all ciphers. A famous example was the machine-based Enigma cipher developed by the Germans in the second world war. Due to its complexity it was thought to be unbreakable, but as is now well known, a team of mathematicians at Bletchley Park, including Alan Turing and Bill Tutte, managed to exploit mathematical patterns in the Enigma machine to crack the cipher.
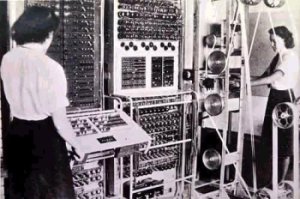
The Colossus Mark II computer was used to break German ciphers during World War II.
This changed the modern world in many ways. Firstly, had the ciphers not been cracked, the Allies may well have lost the war. Secondly, the method of cracking the ciphers involved computers, and the design of the code-breaking Colossus electronic computer by Tommy Flowers ushered in the modern computer age. Modern ciphers, such as the RSA cipher, also rely very heavily upon mathematics, especially the pure mathematics of prime numbers. For example, it is easy to multiply two large prime numbers together, but very hard to find the original two primes given the answer. This asymmetry is used in modern public key ciphers, which are used millions of times every day to keep communications secure.
Personally I find the whole business of security rather dark and I much prefer the subject of making communications as transparent as possible. One of the most important side products of the space race (apart of course from non-stick frying pans) was the development of error correcting codes. In order for a satellite to send back information through a noisy channel and across the vast distances of space, it was essential to find a robust way of making sure that the information got through without error. The answer was again provided by mathematicians, in particular Claude Shannon and Richard Hamming, working at Bell laboratories.
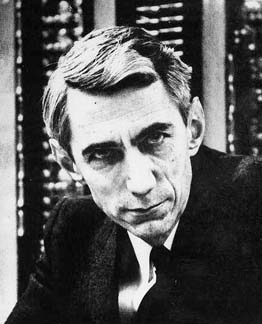
Claude Shannon (1916 - 2001) is today hailed as the father of information theory.
Shannon's seminal contribution was to develop the theory of communication, in which it was possible to predict how much information could be sent through a noisy channel. Hamming's equally important contribution was to work out how to send this information so that if an error occurred the computer receiving it could correct the error itself. In a landmark paper in 1950, he created a family of error-correcting codes now called Hamming codes. These work by creating digital symbols for the various parts of a message which are so different that even if one is corrupted by noise it can still be told apart from any other symbol. The original symbol can then be restored by the computer, and the message corrected. This wonderful idea (which interestingly used mathematics created by the French mathematician Évariste Galois in the 19th century) not only solved the particular problem of communicating a message over long distances, but also opened up a whole new branch of mathematics, that of coding theory. Error correcting codes are now used everywhere, without them we would not be able to transmit pictures or documents over the Internet, phone long distances on a mobile phone, or even listen to music on a CD. Truly they lie at the heart of the technology of the modern world.
Further reading
- Maths in a minute: Modular arithmetic explains how to do addition modulo some number (such as 26),
- Cracking codes explores the arts of code making and code breaking,
- Exploring the Enigma describes the German Enigma machine and how it was cracked,
- Safety in numbers looks at public key cryptography using prime numbers,
- Can you measure information is a series of articles exploring Claude Shannon's contribution to information theory and more,
- Take a break and Communications and ball packing look at error detecting and correcting codes.
About this article

Chris Budd.
This article is adapted from one of Chris Budd's Gresham College lectures, part of a series called Mathematics and the making of the modern and future world. The lectures take place in London, are aimed at a general audience and free to attend.
Chris Budd OBE is Professor of Applied Mathematics at the University of Bath, Vice President of the Institute of Mathematics and its Applications, Chair of Mathematics for the Royal Institution, Gresham Professor of Geometry, and an honorary fellow of the British Science Association. He is particularly interested in applying mathematics to the real world and promoting the public understanding of mathematics.
He has co-written the popular mathematics book Mathematics Galore!, published by Oxford University Press, with C. Sangwin and features in the book 50 Visions of Mathematics ed. Sam Parc.